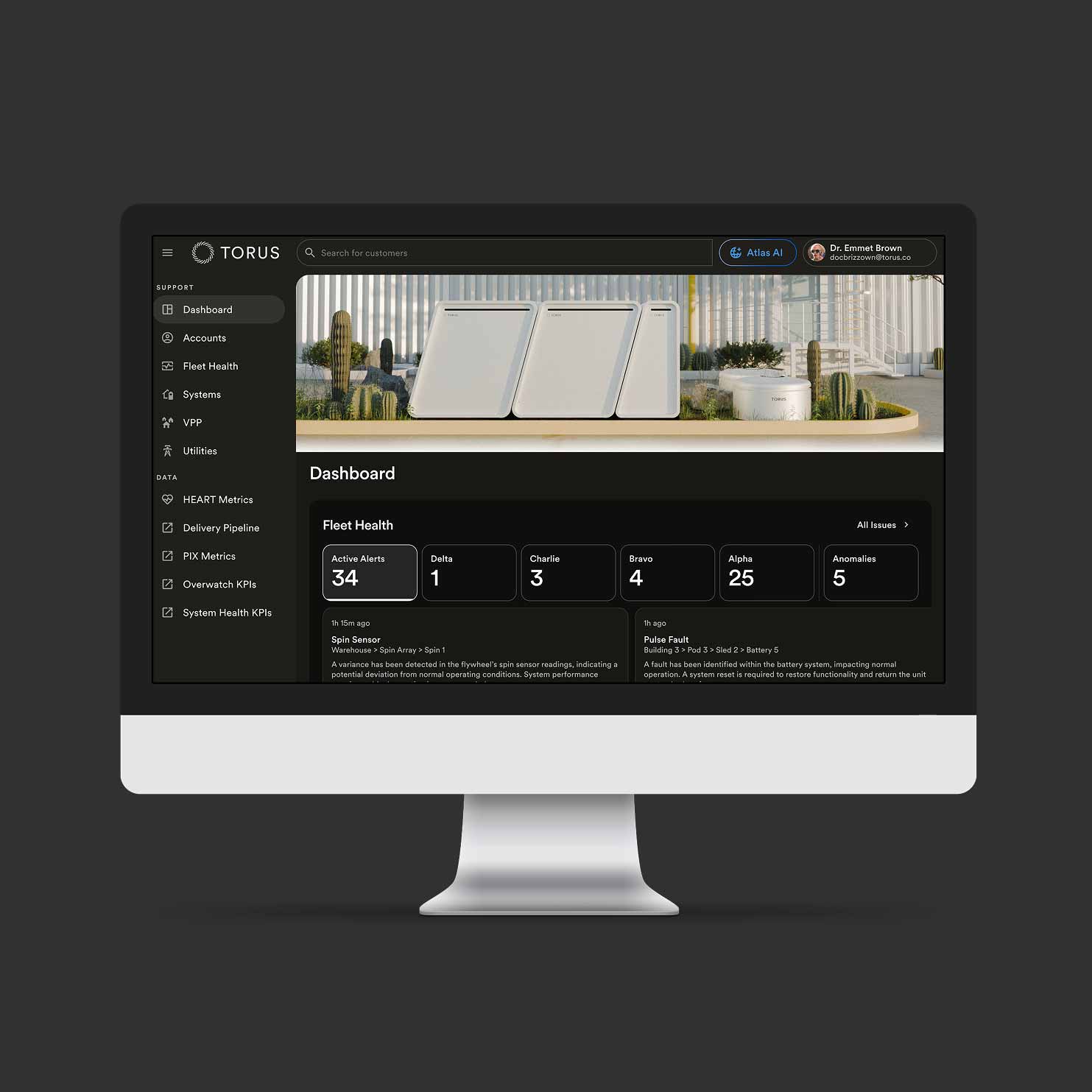
Torus Overwatch keeps every system performing at peak — combining real-time monitoring, proprietary anomaly detection, predictive analytics, and 24/7 response into a single service. Millions of telemetry signals are continuously analyzed and acted on by engineers and certified professionals in the Torus Overwatch Command Center, resolving issues before they impact performance.
Certified operators and analysts
Certified operators and analysts monitoring safety, performance, and cyber defense 24/7. They use AI-powered analytics to monitor, manage, and command the fleet in real time across hardware, firmware, software, and cyber defense layers.
Complete O&M coverage
Overwatch operators and dispatch maintain every Torus Station throughout its full operational life — not just at install. Proactive and predictive maintenance driven by continuous subsecond telemetry keeps systems performing at their peak.
Torus Shield integration
Torus Shield continuously feeds threat intelligence, surveillance, physical security, and behavioral telemetry to Torus Overwatch. Detections and deviations from established baselines are automatically escalated to certified Overwatch operators to validate, triage, and respond.
Grid support and reliability
Torus Overwatch operators continuously monitor performance across every Torus Station, fleet-wide. When grid impacting frequency or voltage variations are detected, Overwatch ensures each station responds appropriately and on time. If a system underperforms or fails to respond as expected, operators intervene directly — helping to maintain grid reliability and preventing power quality issues, brownouts, and blackouts.
Specs and stats
- Telemetry Volume
Millions of data points per system per day
- Analysis Granularity
Sub-second behavioral analysis
- Coverage
Hardware, firmware, software, cybersecurity, and physical security.
- Threat Detection
Actively monitors for known and emerging threat signatures and blocks malicious traffic
- Physical Access
Remote access entry sensors with zero trust protocols


